Scammers are submitting unemployment Gains making use of other people's names and private data. Find out how to protect your self plus your Positive aspects from this kind of identity theft.
In actual fact, it’s accurate to characterize hacking as an in excess of-arching umbrella term for action driving most if not all the malware and malicious cyberattacks over the computing general public, corporations, and governments. Apart from social engineering and malvertising, typical hacking techniques consist of:
How to proceed: Under no circumstances send out money to a person you don’t know. If you think you created a cash transfer or cell application payment into a scammer, Speak to your financial institution or the business you utilized to send the money quickly and inform them that there could are already an unauthorized transaction. You can even file a grievance Along with the FBI’s Net Criminal offense Criticism Center at
A brute drive assault is often a demo-and-mistake approach danger actors use to crack passwords or encryption keys by systematically trying each and every doable mix until finally the correct a person is found. It could be time-consuming but is usually successful versus weak or straightforward passwords.
Report the fraudulent transaction to the corporation behind the funds transfer application and talk to them to reverse the payment. Should you connected the app to some bank card or debit card, report the fraud to the charge card organization or bank. Request them to reverse the cost.
Leverage encryption – Whether or not hackers correctly access a company's community, encryption can correctly avert them from breaching or accessing any data.
In a fascinating twist, Emotet has developed from currently being a banking Trojan in its possess right into a Instrument for offering other malware, including other banking Trojans like Trickbot.
Ethical hackers also can perform vulnerability assessments, review malware to gather menace intelligence or be involved in protected computer software growth lifecycles.
Trojans continue being a risk to enterprises, with many of the most effectively-identified currently being Emotet and TrickBot. Emotet, Trickbot, and GandCrab all depend upon malspam as their Key vector of infection. These destructive spam email messages, disguised as common models, trick your finish consumers into clicking destructive obtain hyperlinks or opening an attachment loaded with malware.
But Speak to the company you accustomed to send The cash and inform them it absolutely was a fraudulent transaction. Question them to reverse the transaction, if possible.
Conducting company espionage for employ, stealing intellectual house or other private facts from their shopper enterprise’s competition.
Cell phone hackers use several different strategies to access someone’s mobile phone and intercept voicemails, phone calls, textual content messages, and in many cases the mobile phone’s microphone and digicam, all devoid of that user’s authorization and even know-how.
Español Scammers are regularly acquiring get more info new tips on how to steal your cash, from blackmail to romance scams to marketing nonexistent things. Understand the warning signs of typical fraud and scams so you can guard by yourself and others.
WHO has a constitutional mandate to "establish, build and boost Global expectations with respect to Organic, pharmaceutical and equivalent goods".
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now!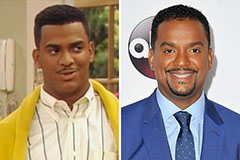 Alfonso Ribeiro Then & Now!
Alfonso Ribeiro Then & Now! Jeremy Miller Then & Now!
Jeremy Miller Then & Now! Richard Thomas Then & Now!
Richard Thomas Then & Now! Bill Murray Then & Now!
Bill Murray Then & Now!